The latest report on the Axie Infinity/ Ronin bridge hack is too good to be true. Especially considering the FBI claims a North Korea-sponsored hacking group is responsible for it. “A senior engineer at Axie Infinity was duped into applying for a job at a company that, in reality, did not exist,” The Block reports. That’s not all, apparently, the hackers’ spyware got into the system through a simple .pdf file. Unbelievable that a $622M hack started that way.
The Ronin Network is an Ethereum sidechain that exclusively serves Axie Infinity. Both a billion-dollar business and a fun app with a thriving internal economy and an international audience, the play-to-earn game was one of the bull market’s biggest success stories. Sky Mavis is the studio behind Axie Infinity. And one of its programmers apparently fell victim to the simplest social engineering trick in the book.
Is North Korea To Blame?
According to surveillance firm Chainalysis, North Korea-sponsored hackers stole over $400M in 2021 alone. And according to the FBI, they’re responsible for the Axie Infinity/ Ronin hack. The alphabet agency traced the funds to wallets associated with North Korean hacking group Lazarus. Does The Block’s article complete or negate this version of the story? It’s hard to see North Koreans pulling a stunt quite like this.
In any case, at the time the FBI was extremely clear in a statement quoted here:
“Through our investigation we were able to confirm Lazarus Group and APT38, cyber actors associated with the DPRK, are responsible for the theft of $620 million in Ethereum reported on March 29th.”
If true, they broke their 2021 record with just one operation.
How Did The Axie Infinity/ Ronin Hack Happen?
The hack’s supposed story is hilarious, to say the least. According to The Block:
“Earlier this year, staff at Axie Infinity developer Sky Mavis were approached by people purporting to represent the fake company and encouraged to apply for jobs, according to the people familiar with the matter.”
After several rounds of interviews, one of Sky Mavis’ developers got an extremely generous offer. He opened up Pandora’s box and all hell broke loose.
“The fake “offer” was delivered in the form of a PDF document, which the engineer downloaded — allowing spyware to infiltrate Ronin’s systems. From there, hackers were able to attack and take over four out of nine validators on the Ronin network — leaving them just one validator short of total control.”
To complete the attack, they took control of another entity. Once upon a time, “the Axie DAO allowlisted Sky Mavis to sign various transactions on its behalf.” The permissions were still valid and the hackers took advantage of them. The Ronin bridge’s operators’ post-mortem on the attack describes the fallout.
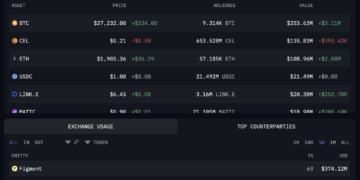
“The attacker managed to get control over five of the nine validator private keys — 4 Sky Mavis validators and 1 Axie DAO — in order to forge fake withdrawals. This resulted in 173,600 Ethereum and 25.5M USDC drained from the Ronin bridge in two transaction”
Did Lazarus’ operators orchestrate such a Hollywoodesque attack? Or does the comedic modus operandi implicate other perpetrators?
AXS price chart on FTX | Source: AXS/USD on TradingView.com
Previous Coverage Of The Axie Infinity/ Ronin Hack
Let’s turn to archival material to complete the story and add extra detail. After the breach happened, NewsBTC reported on Axie Infinity and Sky Mavis’ first solution to the problem:
“The latest move announced is a $1 million bug bounty program that invites white hat hackers to stress test the blockchain.
Co-Founder and COO of Sky Mavis and Axie announced: “Calling all whitehats in the blockchain space. The Sky Mavis Bug Bounty program is here. Help us keep the Ronin Network secure while earning a bounty up to $1,000,000 in bounty for fatal bugs.”
And then, when operators reopened the new and improved Ronin bridge, our sister site Bitcoinist reviewed its characteristics:
“In addition to the two independent audits on its smart contracts, the Ronin Bridge’s new design has implemented a new “circuit-breaker” feature. This was directly added to prevent a bad actor from replicating the previous attack or exploiting any potential new attack vector.”
So, the Ronin bridge seems to be safe to use at the moment. It also seemed to be safe to use before the hack, though. Do your own research and be safe out there.
Featured Image by Niek Verlaan from Pixabay | Charts by TradingView
Credit: Source link